The Internet Meltdown: Who Really Attacked X?
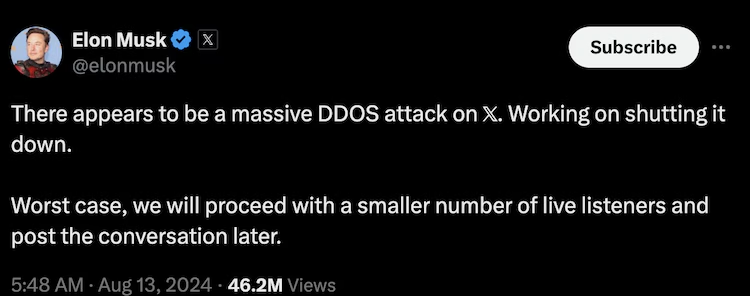
Elon Musk says X was knocked offline by ‘ddos-attack’ . Elon Musk’s social media giant, X (formerly known as Twitter), found itself under siege on Monday as a massive cyberattack took down services worldwide. But the big question remains: who was behind it? Musk, never one to hold back, pointed fingers toward the “Ukraine area,” while a pro-Palestinian hacker group, Dark Storm Team, claimed responsibility. Was this a case of cyber warfare, political maneuvering, or something even more sinister?
Musk’s Bold Allegations
- On Tuesday, Musk claimed X was targeted in a “massive cyberattack” with IP addresses tracing back to the “Ukraine area.”
- The platform suffered repeated global outages, frustrating users and raising concerns about cybersecurity.
- During an interview with Fox News’ Larry Kudlow, Musk admitted, “We’re not sure exactly what happened, but this was a massive cyberattack to bring down the X system.”
Hacktivists, Governments, or Something Else?
As Musk’s statement gained traction, cybersecurity experts and political analysts started questioning the narrative. The pro-Palestinian hacker group Dark Storm Team openly took credit for the attack in a Telegram post. The group, known for targeting nations and entities aligned with Israel, has a history of launching cyber offensives.
But here’s the twist—Musk didn’t directly acknowledge the group’s claim. Instead, he fueled speculation that a well-coordinated force, possibly backed by a nation-state, was responsible. “We get attacked every day, but this was different. This took a lot of resources—either a highly organized group or a country was behind it,” Musk posted on X.
Cybersecurity professionals, however, were skeptical. Many noted that DDoS (Distributed Denial-of-Service) attacks, the kind that flooded X’s servers, don’t necessarily require massive resources. A handful of well-organized hackers with the right tools can unleash chaos.
Inside the Attack: What Really Happened?
- The outages started at 9:45 UTC, with waves of malicious traffic bombarding X’s infrastructure.
- Downdetector reported 39,021 users in the U.S. experiencing disruptions at its peak.
- By 5 PM ET, disruptions had decreased to about 1,500 users, showing signs of recovery.
- A confidential source in the internet infrastructure industry confirmed that the attack came in “multiple waves,” overwhelming the system temporarily.
DDoS attacks work by overwhelming a target with fake traffic, making services inaccessible. While disruptive, they don’t typically involve hacking into data or breaching security. That raises an important question—was this just a nuisance attack, or a test for something bigger?
Musk’s Ukraine-Russia Tensions: Coincidence or Connection?
It’s no secret that Musk has been vocal about Ukraine’s war against Russia. His Starlink satellite system remains critical to Ukraine’s military communications, yet Musk has been openly critical of prolonged warfare.
- He recently claimed Ukraine’s “entire front line would collapse” without Starlink’s support.
- Musk has also taken heat for allegedly favoring de-escalation rather than outright Ukrainian victory.
- Critics accused him of “targeting Zelenskyy instead of Putin,” to which Musk responded: “I literally challenged Putin to one-on-one combat over Ukraine.”
While it’s unclear whether the cyberattack was retaliation, an intimidation tactic, or just another battle in the chaotic digital war, Musk’s comments have undeniably added fuel to an already raging fire.
The Fallout: What’s Next for X?
With the world more interconnected than ever, cyberattacks on major platforms aren’t just a tech problem—they’re a global security issue. Musk’s claim that a “large entity” may have been involved raises concerns about future digital warfare. Could we see more sophisticated cyberattacks aimed at controlling the narrative on social media? Could adversaries be testing the vulnerabilities of private infrastructure?
For now, X has managed to restore services, but the bigger question remains: was this just a warning shot? And more importantly, who will be next?
Stay tuned as the drama unfolds, because in the world of tech, politics, and cyberwarfare, nothing is ever as simple as it seems.
Understanding DDoS Attacks: A Complete Guide
Introduction
A Distributed Denial of Service (DDoS) attack is a malicious attempt to disrupt the normal traffic of a targeted server, service, or network by overwhelming it with a flood of internet traffic. These attacks can cause severe financial and operational damage to businesses, government institutions, and individuals.
What is a DDoS Attack?
DDoS attacks exploit multiple compromised computer systems as sources of attack traffic. These could include computers, IoT devices, and cloud-based services. The attacker controls these compromised devices to send a large volume of requests to a single target, causing it to slow down or become entirely unresponsive.
Types of DDoS Attacks
1. Volume-Based Attacks
These attacks flood the target with massive amounts of data to consume bandwidth. Examples include:
- UDP Flood
- ICMP (Ping) Flood
- DNS Amplification
2. Protocol Attacks
These attacks consume server resources by exploiting weaknesses in network protocols. Examples include:
- SYN Flood
- Ping of Death
- Smurf Attack
3. Application Layer Attacks
These attacks target specific applications or web servers to exhaust resources. Examples include:
- HTTP Flood
- Slowloris Attack
- DNS Query Flood
How DDoS Attacks Work
A DDoS attack typically follows these steps:
- Infecting Devices – Attackers use malware to compromise multiple devices.
- Creating a Botnet – Compromised devices form a network of bots under attacker control.
- Launching the Attack – Attackers instruct the botnet to send overwhelming traffic to the target.
- Crippling the Target – The victim’s server crashes or becomes slow, affecting business operations.
Impact of DDoS Attacks
1. Financial Losses
Businesses lose revenue due to downtime and the cost of mitigation.
2. Reputation Damage
Customers lose trust in an organization that frequently suffers from DDoS attacks.
3. Data Breaches
Some DDoS attacks serve as a smokescreen for data theft.
4. Operational Disruptions
IT teams may struggle to restore services, leading to extended downtimes.
How to Mitigate DDoS Attacks
1. Use a DDoS Protection Service
Services like Cloudflare, Akamai, and AWS Shield provide robust defenses against attacks.
2. Deploy Firewalls and Intrusion Detection Systems
These help filter malicious traffic and prevent unauthorized access.
3. Rate Limiting and Traffic Filtering
Restricting the number of requests a user can make prevents excessive traffic.
4. Network Redundancy and Load Balancing
Distributing traffic across multiple servers can prevent a single point of failure.
5. Monitor Network Traffic
Using monitoring tools like Wireshark and Splunk can help detect unusual spikes in traffic.
Preventing Future DDoS Attacks
1. Keep Software Updated
Regularly update firewalls, operating systems, and security patches.
2. Implement Strong Access Control
Restrict access to essential systems and monitor user activities.
3. Educate Employees
Cybersecurity awareness can help employees recognize potential threats.
4. Use Web Application Firewalls (WAFs)
WAFs help filter and monitor HTTP traffic to block suspicious requests.
Conclusion
DDoS attacks are a growing cybersecurity threat that can cripple businesses and individuals. Understanding different attack types, their impact, and mitigation strategies can help organizations stay protected. Investing in robust security solutions and staying vigilant is key to preventing DDoS disruptions.



Pingback: Reacher Season 3 - watch full episodes (2025) Download